Governance determines the velocity of safe adoption. Unregulated AI leads to shadow IT and data leaks, posing numerous challenges to businesses. In GoInsight.AI, we believe that a compliant and governed environment is essential to turn AI from an experimental tool into an enterprise asset. Here, the security and compliance features, including control access, encryption, and audit, can help organizations secure their AI future.
Full Control Over Data and AI Models. Decouple proprietary IP from public training loops and enforce strict cryptographic standards to secure the inference lifecycle.
Fine-Grain Access Control & Governance. Bind execution rights to enterprise identity protocols, enforcing real-time, Zero-Trust authorization for every interaction.
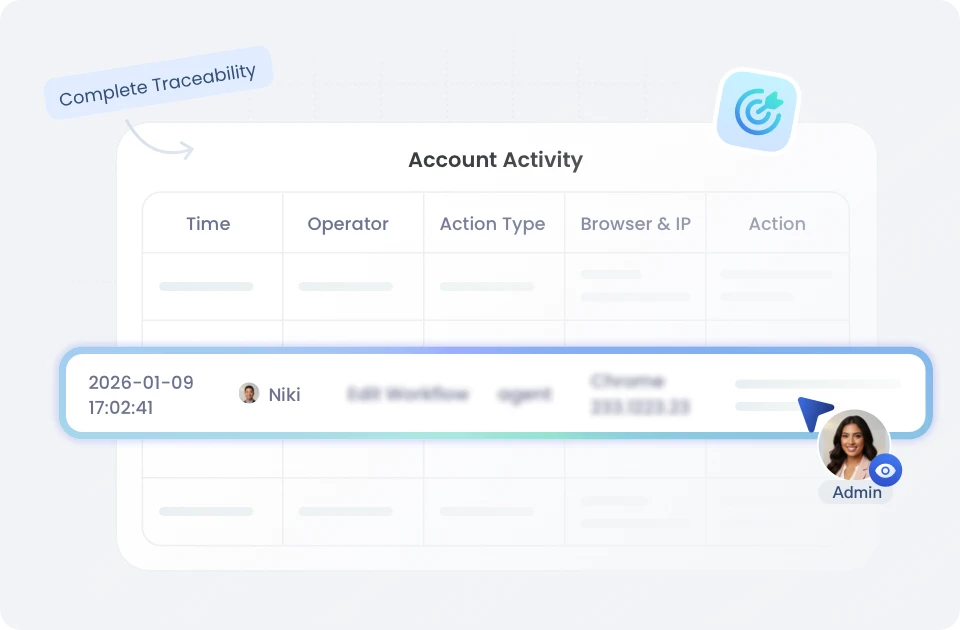
Audit Trails & Monitoring for Compliance. Shift from passive logging to forensic traceability, creating an immutable evidence chain for incident investigation and regulatory defense.
Full Control Over Data and AI Models
-
 Zero-Training Guarantee
Zero-Training Guarantee Use the secure, fast, and efficient AirDroid Business mobile device management and remote control solutions in the Cloud for rapid deployment and flexible expansion.
-
 Enterprise LLM Compliance
Enterprise LLM Compliance Support enterprise-grade model providers, such as Azure OpenAI, and ensure all model interactions operate under a strict enterprise compliance framework.
-
 End-to-End Data Encryption
End-to-End Data Encryption End-to-end data encryption secures all data at rest using AES-256 standards and protects data in transit with TLS 1.2+ encryption across all communications.
-
 Secure Deployment Options
Secure Deployment Options Deployment options ensure security through SaaS (with regional data residency) or self‑hosted solutions (planned) for full isolation within your VPC or private cloud.
-
 GDPR Alignment (Model-dependent)
GDPR Alignment (Model-dependent) GoInsight.AI can operate in alignment with GDPR when using compliant backends, like Azure OpenAI, in appropriate regions. Please note that other providers or regions may not offer equivalent guarantees, and customers remain responsible for their compliance and data residency choices.
-
 ISO/IEC 42001 Alignment (Planned)
ISO/IEC 42001 Alignment (Planned) We’re aligning our security and AI governance with ISO/IEC 42001 and working toward certification, reinforcing our commitment to globally recognized best practices.

Fine-Grain Access Control & Governance
Provide you with precise access control for enterprise identity integration, multi-factor security, and real-time authorization to ensure that only the right people and systems can access critical workflows and assets.
- Zero-Trust Access Control: Every call to a Flow, Bot, Tool, or Knowledge Base undergoes real-time authorization verification based on the caller's identity, role, and resource ACL (Access Control List).
- SSO Integration (Planned): GoInsight.AI will support integration with enterprise Identity Providers (IdPs), allowing you to apply your existing identity policies and manage employee access with a single sign-on experience.
- MFA Enforcement (Planned): GoInsight.AI will support mandatory Multi-Factor Authentication (MFA), adding an extra layer of protection to account logins and reducing the risk of credential compromise.
Provides detailed audit logs and process controls to investigate incidents, meet regulatory requirements, and govern automation responsibly.
Business Continuity & Monitoring
Business Continuity Assurance: High Availability (HA) architecture for key service components deployment, eliminating single points of failure and ensuring consistent business uptime. Meanwhile, we maintain a defined disaster recovery plan and run regular failover drills to ensure data and services can be quickly restored in extreme situations.
24/7 Monitoring & Scanning: We provide 24/7 real-time monitoring and automated alerts covering service health, error rates, and performance metrics. Additionally, we perform continuous automated vulnerability scanning on platform components. Identified high-risk vulnerabilities are managed with a remediation process and strict SLA limits.
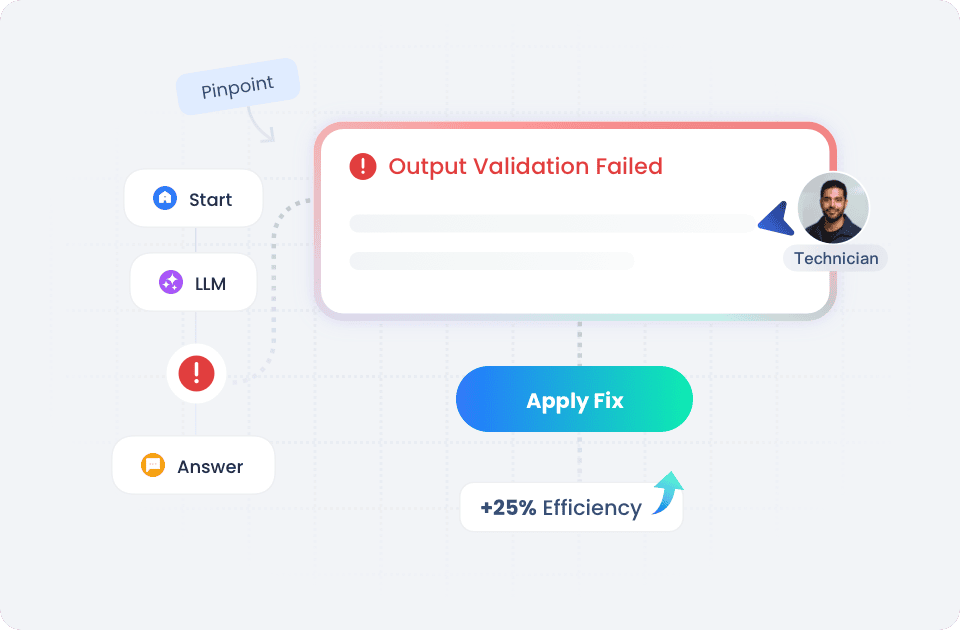
Audit & Controlled Automation
Full-Chain Audit Logs: We provide complete traceability capabilities by recording in detail who took what action to which resource and when. These logs support on-demand filtering and exporting to provide a chain of evidence for security incident investigations and internal audits.
Granular Token & Data Auditing: Auditing extends down to each AI interaction. Every model call is logged with details such as model version, token usage, originating Flow/Bot, and the operator, allowing you to fully trace the workflow and understand exactly what the AI executed.
Human-in-the-Loop (Planned): Humans are always the gatekeepers for high-risk automation. You can enforce "human approval" nodes to require human approval before the AI proceeds for workflows involving sensitive data or critical actions.
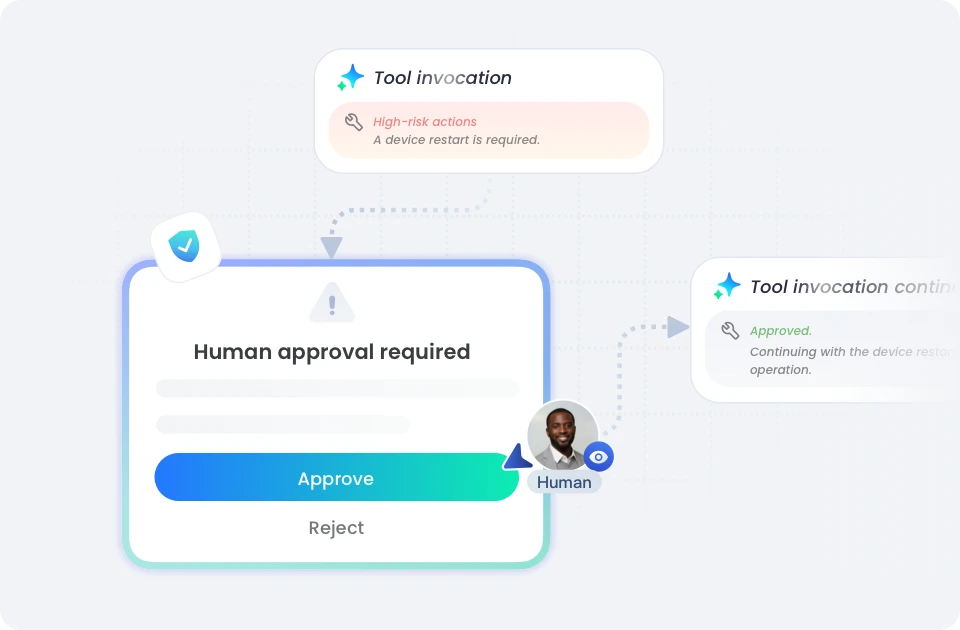
Traceability for Audits
Based on the full-chain audit logs and granular Token records, we provide a complete traceable chain of evidence for your internal audits, external audits, and incident investigations.